Client-Server Architecture: Distributing Tasks Between Requesters and Providers
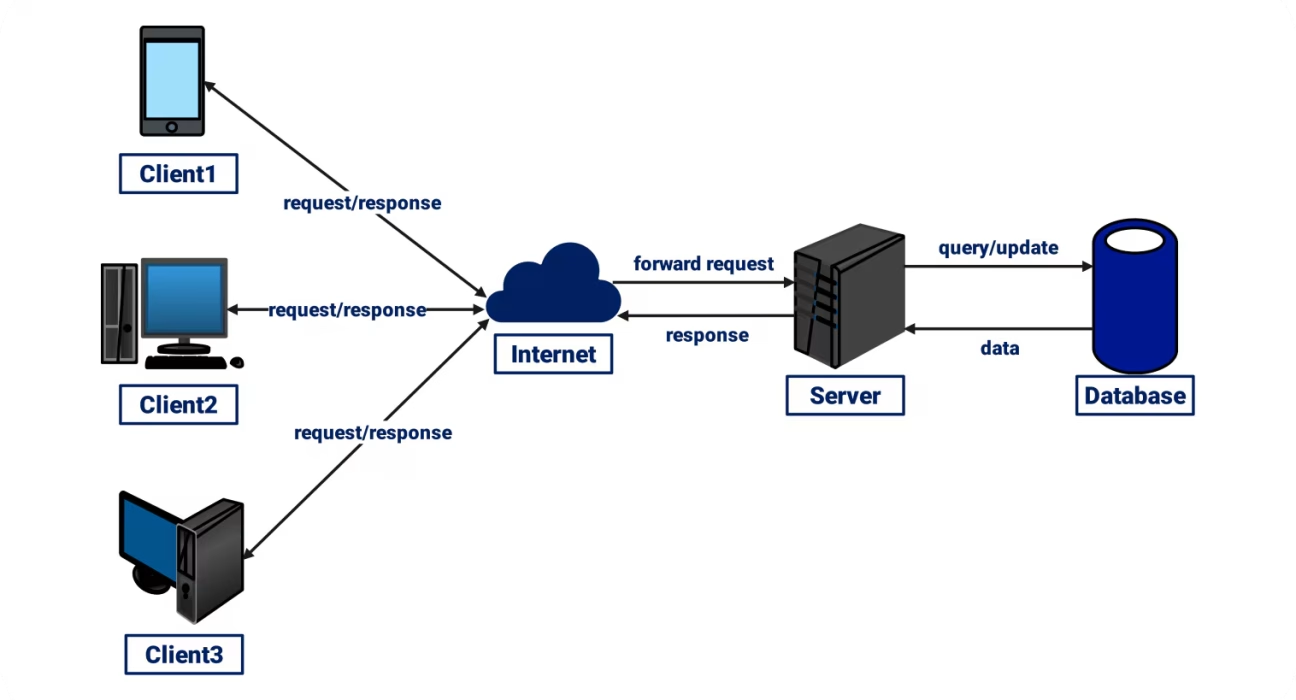
Modern digital services work because tasks are split sensibly between the device a person uses and the systems that sit behind the service. That split is called client-server architecture. The “client” requests a service (a web page, an API response, a file, or a transaction). The “server” provides it by running business logic, accessing data, and enforcing security rules. If you are learning web development through a full stack developer course in coimbatore, this architecture is one of the first concepts that explains why applications are designed the way they are.
Why Client-Server Architecture Exists
At its core, client-server architecture is about centralising resources and standardising access. Users may connect from different devices-browsers, mobile apps, desktop applications- but the organisation typically wants a single source of truth for data and rules. When the server owns the data store and the business logic, updates can be deployed once and used by everyone.
This approach also supports governance and compliance. Centralised servers can apply consistent authentication, authorisation, logging, and auditing. Instead of trusting each client device to behave correctly, the server assumes clients can be unreliable or even malicious, and validates requests before taking action.
Key Components and the Request–Response Flow
What the Client Does
A client is any “service requester.” In many web systems, this is a browser running a front-end application. In mobile-first products, it is an Android or iOS app. The client is responsible for:
- Presenting the user interface and collecting user input
- Making network calls to servers (often via HTTP/HTTPS)
- Handling responses and updating the UI
- Doing limited local processing (for speed and responsiveness)
What the Server Does
A server is the “service provider.” It can mean an application server, a database server, a file server, an authentication server, or a combination. Typical responsibilities include:
- Enforcing business rules (pricing, eligibility, workflows)
- Reading and writing persistent data
- Performing secure operations (payments, identity checks)
- Coordinating with other internal or third-party services
How Communication Usually Works
Most client-server systems follow a request–response pattern:
- The client sends a request (for example, “get product list” or “submit payment”).
- The server authenticates the request and validates input.
- The server runs logic, fetches or updates data, and prepares a response.
- The client receives the response and renders it for the user.
For real-time use cases (chat, trading dashboards, live logistics tracking), systems may use long polling or persistent connections such as WebSockets, but the fundamental roles remain the same: clients request, servers provide.
Designing the Boundary: What Runs on Client vs Server
A common design question is: Where should a task live? The answer depends on trust, performance, and maintainability.
Keep Trusted Decisions on the Server
Anything that affects money, permissions, or sensitive data should be decided server-side. For example:
- Discount eligibility and final pricing
- Role-based access control (what a user can view or change)
- Fraud checks and transaction approval
Even if the client performs preliminary checks for user convenience (like showing “password too short”), the server must enforce the final rules.
Use the Client for Responsiveness
Clients can improve perceived performance by:
- Rendering UI locally (single-page applications)
- Caching small amounts of non-sensitive data
- Debouncing user input and reducing unnecessary requests
A practical example is an e-commerce “Add to cart” action. The client updates the cart badge instantly, while the server confirms stock availability and reserves inventory. The user experience stays fast, but the server remains the authority.
Scalability and Reliability Patterns in Client-Server Systems
As usage grows, server-side load becomes the main bottleneck. Mature client-server systems adopt patterns that keep the service stable and predictable.
Horizontal Scaling and Stateless Servers
If application servers are stateless, meaning they do not store user session data in memory, they can scale horizontally. A load balancer can distribute incoming requests across many identical servers. Session state, if needed, is stored in shared systems such as databases or distributed caches.
Caching and Content Delivery
Caching reduces repeated work:
- Browser caching avoids re-downloading unchanged assets
- Reverse proxies reduce repeated server computation
- CDNs serve static content close to users, reducing latency
Asynchronous Work and Queues
Some tasks should not block a user request, such as sending emails, generating reports, or processing large imports. These are often delegated to background workers via message queues. The client receives a quick acknowledgement, while the server processes the heavy task reliably in the background.
Security and Trust: The Server Must Assume the Client Can Lie
A key rule in client-server architecture is: never trust the client. Security is not a feature you “add later”; it is shaped by the architecture itself.
Servers must enforce:
- Transport security (TLS/HTTPS) to protect data in transit
- Strong authentication (session cookies or tokens)
- Authorisation checks on every protected action
- Input validation and safe error handling
- Rate limiting to reduce abuse and denial-of-service risk
Clients support security through safe storage practices and careful UI design, but the final enforcement always belongs to the server.
Conclusion: Client-Server Architecture as a Practical Set of Trade-offs
Client-server architecture remains the backbone of most web and mobile systems because it balances user experience with control, security, and maintainability. Clients focus on interaction and responsiveness; servers focus on data integrity, business rules, and secure operations. Once you understand where to place responsibilities and why, you can design systems that scale and stay reliable as requirements change. For learners coming through a full stack developer course in coimbatore, mastering these boundaries is what turns “working code” into production-ready engineering.










